
What Is TOR ?
Tor Is A Secure Web Brouser Its A Simple But Unique All Big Hackers Mostly Use TOR,
TOR Full Name Is "Technical Onion Router"
He's The Number One Secure Brouser Because This Hide Ur Information Then The Google Is Never Known Youre Itendity.
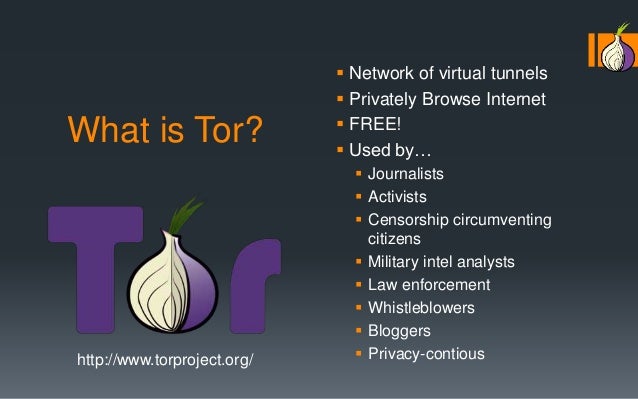
Tor is free software for enabling anonymous communication. The name is derived from an acronym for the original software project name "The Onion Router.
How To Use ?
Its very Simple U Can Download Its Free Not Charges And U Simple Install And Run And Go URL Bar And Type Website URL .
Install and configure Tor Browser. Start by downloading and installing Tor Browser. ...
Get online with Tor. ...
Choose your security level. ...
Rethink your browsing habits. ...
Understand Tor circuits. ...
Create a new identity. ...
Use HTTPS. ...
Access .onion sites.
Why Hackers Use It ?

Because Its hide Your Identity And Secure You All Web And Hackers And Anyone Never Know Your Identity And Its For manuall For Hackers, The Tor network is a group of volunteer-operated servers that allows people to improve their privacy and security on the Internet. Tor's users employ this network by connecting through a series of virtual tunnels rather than making a direct connection, thus allowing both organizations and individuals to share information over public networks without compromising their privacy. Along the same line, Tor is an effective censorship circumvention tool, allowing its users to reach otherwise blocked destinations or content. Tor can also be used as a building block for software developers to create new communication tools with built-in privacy features.
Individuals use Tor to keep websites from tracking them and their family members, or to connect to news sites, instant messaging services, or the like when these are blocked by their local Internet providers. Tor's onion services let users publish web sites and other services without needing to reveal the location of the site. Individuals also use Tor for socially sensitive communication: chat rooms and web forums for rape and abuse survivors, or people with illnesses.
Journalists use Tor to communicate more safely with whistleblowers and dissidents. Non-governmental organizations (NGOs) use Tor to allow their workers to connect to their home website while they're in a foreign country, without notifying everybody nearby that they're working with that organization.
Groups such as Indymedia recommend Tor for safeguarding their members' online privacy and security. Activist groups like the Electronic Frontier Foundation (EFF) recommend Tor as a mechanism for maintaining civil liberties online. Corporations use Tor as a safe way to conduct competitive analysis, and to protect sensitive procurement patterns from eavesdroppers. They also use it to replace traditional VPNs, which reveal the exact amount and timing of communication. Which locations have employees working late? Which locations have employees consulting job-hunting websites? Which research divisions are communicating with the company's patent lawyers?
A branch of the U.S. Navy uses Tor for open source intelligence gathering, and one of its teams used Tor while deployed in the Middle East recently. Law enforcement uses Tor for visiting or surveilling web sites without leaving government IP addresses in their web logs, and for security during sting operations.
The variety of people who use Tor is actually part of what makes it so secure. Tor hides you among the other users on the network, so the more populous and diverse the user base for Tor is, the more your anonymity will be protected.




No comments:
Post a Comment